How to deliver awareness training at scale for many clients
How to deliver awareness training at scale for many clients without turning every MSP campaign into admin drag.
DefendWise
DefendWise
TL;DR
How to deliver awareness training at scale for many clients is an operating model question, not a content-library question.
An MSP can have good videos, good phishing templates, and good intentions, then still lose margin because every client needs separate setup, reminders, reports, branding, and evidence.
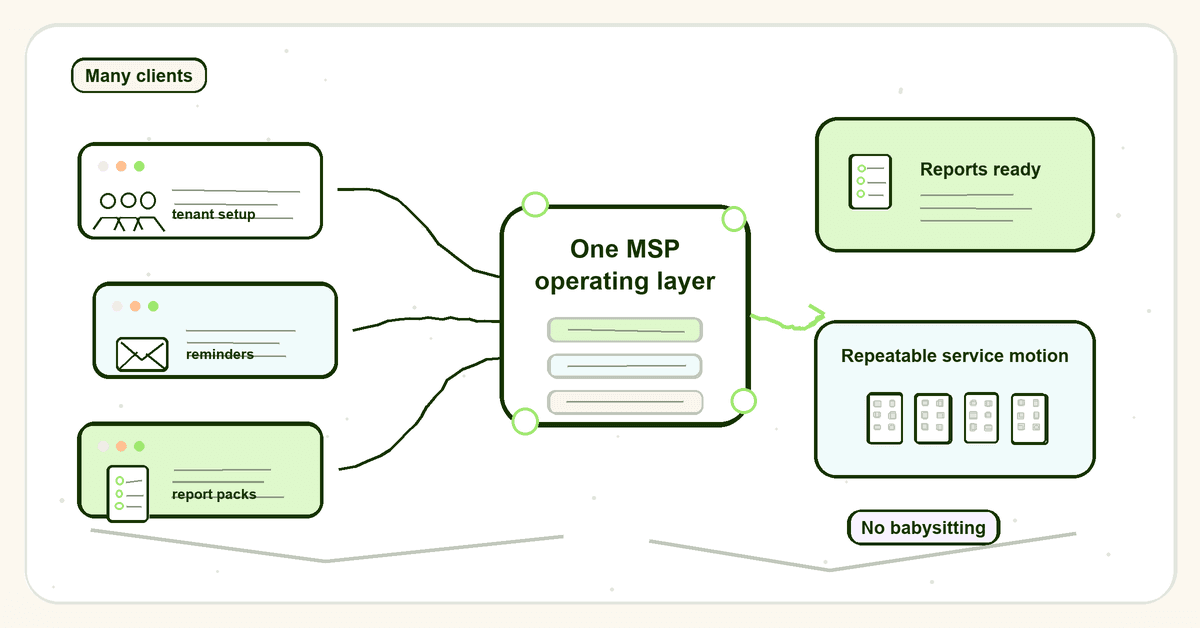
The scalable model is simple to describe and harder to build: one MSP operating layer, clean tenant separation, reusable campaign standards, automated user lifecycle, recurring reminders, client-ready reports, and framework-aware evidence.
If training only works when a technician babysits each tenant, it does not scale. It just travels poorly.
What awareness training at scale means for MSPs
For an internal IT team, scaling awareness training usually means reaching more employees inside one company.
For an MSP, it means something different.
You are not training one workforce. You are training many workforces, under many brands, with different user lists, risk levels, compliance asks, renewal dates, executives, and reporting expectations.
That changes the job.
A client owner does not care that your SAT vendor has 1,000 modules if their staff never complete the right campaign. A vCISO does not care that phishing simulations exist if evidence cannot be exported before an audit. Your service manager does not care that training looks slick if the team spends Friday chasing 14 overdue users across 9 portals.
At MSP scale, the unit of work is not a module. It is a repeatable client delivery system.
That system needs to answer 6 questions every month:
- Which clients are covered?
- Which users are in scope?
- Which campaigns are assigned?
- Who has not finished?
- What evidence can be shown to the client, insurer, or auditor?
- How much human admin did the MSP spend to get there?
If those answers live in scattered spreadsheets, mailbox searches, and screenshots, the program may exist, but it is not scaled.
Why awareness training breaks across many clients
Security awareness training is no longer a nice-to-have line item. Frameworks, insurers, and clients expect it.
NIST CSF 2.0 includes awareness and training under Protect. The PR.AT category says personnel are provided cybersecurity awareness and training so they can perform cybersecurity-related tasks. NIST's Protect mapping also ties PR.AT to publications such as SP 800-50 and SP 800-84.
NIST SP 800-50 Rev. 1 takes the point further. It frames cybersecurity and privacy learning as a lifecycle program that should be managed, measured, updated, and tied to behavior change. That is a better mental model for MSPs than "send a video once a year."
The threat case is not theoretical either. Verizon's 2025 DBIR archive page keeps pointing readers back to human-heavy causes such as phishing, social engineering, and stolen credentials. Its 2025 SMB snapshot shows social engineering remained a named breach pattern for small and medium businesses.
The scaling problem comes from the gap between those expectations and the way many MSPs try to deliver the service.
1. The work multiplies by tenant.
One client campaign might be easy. Add 30 clients and the same task becomes user imports, exceptions, reminder edits, report exports, and status checks across 30 different business contexts.
That is where margin disappears. The MSP sells training as part of a fixed-fee security package, then delivers it as a manual project every month.
2. Reporting becomes the service.
The client rarely asks to inspect every module. They ask, "Who has done it?" "What are we behind on?" "Can I show this to my insurer?" "Can you send this before our ISO review?"
The FTC's small business cybersecurity guidance tells businesses to train staff on a regular schedule and track participation. It even suggests considering network access consequences for employees who do not attend training. That makes reporting and participation tracking part of the control, not an afterthought.
3. Framework language turns into client anxiety.
CIS Control 14 calls for a security awareness program that influences workforce behavior and reduces risk. ISO/IEC 27001 frames information security management as a risk management system across people, process, and technology.
Most SMB clients do not speak in control numbers. They speak in stress: "Are we covered?" "Will this satisfy the questionnaire?" "Can you show proof?"
An MSP at scale needs to translate controls into simple client proof without rebuilding the explanation every time.
4. Admin-friendly is now table stakes.
Even other MSP-focused SAT vendors now lead with multi-tenancy, automation, reports, and managed admin. Huntress announced SAT features around managed programs, directory setup, multi-tenancy onboarding, and monthly automated reports. CyberHoot markets MSP automation, multi-customer tenancy, reminders, and reports. Hook Security leads with multi-tenant dashboards and portfolio-wide deployment.
That pattern matters. The market has noticed the same pain: content alone does not remove the MSP delivery load.
The MSP operating model for awareness training at scale
A scalable awareness program has 4 layers: tenant, user, campaign, and proof.
The mistake is treating those layers as separate chores. They need to work as one delivery motion.
| Operating layer | What must be standardized | What stays client-specific | Evidence the MSP should produce |
|---|---|---|---|
| Tenant setup | Naming, owner contacts, default cadence, reporting schedule, branding checklist | Client logo, domains, executive contacts, compliance context | Tenant setup record, campaign scope, branding status |
| User lifecycle | Import or sync method, groups, joiner and leaver handling, overdue rules | Exclusions, high-risk users, privileged users, seasonal staff | User roster, assigned users, completion and overdue status |
| Campaign delivery | Baseline topics, due dates, reminders, escalation path, completion rules | Industry examples, client policies, executive messaging | Campaign log, assignment dates, reminder history, module list |
| Reporting | Monthly summary format, QBR roll-up, evidence pack fields | Client-facing notes, framework references, stakeholder view | Client report, exportable evidence, audit-ready completion record |
| Service review | Internal exception review, risk notes, follow-up tasks | Client decisions, accepted risks, special requests | Action list, QBR notes, renewal packaging inputs |
This is why multi-tenant delivery matters. It is not a dashboard preference. It is the difference between a service line and a collection of one-off jobs.
A good MSP model keeps the delivery spine consistent while leaving enough room for client context.
That means every client gets a known baseline: onboarding, core cyber hygiene, phishing and social engineering, reporting suspicious activity, password and MFA behavior, business email compromise, safe file handling, and data handling basics.
Then higher-risk users get extra attention. Finance gets payment-change and invoice-fraud training. Admins get privileged access behavior. Executives get impersonation and travel-risk scenarios. Developers get secure coding or product risk topics where relevant.
The MSP should not have to invent that structure from scratch for every tenant.
How to deliver awareness training at scale for many clients
1. Define the standard client package before touching the platform
Start with the offer, not the tool.
Write down what every client gets by default: annual baseline training, monthly or quarterly micro-training, phishing or social engineering exercises if included, monthly completion reporting, and an evidence pack on request.
This protects the MSP from custom-work creep. Without a standard package, every client conversation creates a different version of the service.
The package should also name what is not included. For example, bespoke policy writing, custom role-based modules, incident workshops, or audit consulting may sit outside the base training service.
2. Build a tenant setup checklist
Every client tenant should be created the same way.
Use a checklist for client name, primary admin contact, reporting contact, brand assets, sending domain needs, user source, excluded users, launch date, reminder cadence, escalation path, and framework context.
This is unglamorous work. It is also the work that stops reports landing with the wrong logo, campaigns going to former staff, and evidence being impossible to trace later.
For MSPs, white-label delivery matters because the client should experience training as part of the MSP's service, not as a random third-party portal. But branding cannot become a manual art project every time. It needs a repeatable setup motion.
3. Automate the user lifecycle first
User lists are where scaling plans usually break.
A static CSV can work for a pilot. It does not work well across many growing clients unless someone owns the cleanup. Joiners miss training. Leavers remain assigned. Name changes create duplicate users. Seasonal staff muddy the report.
If possible, sync users from the client's identity source. If not, set a clear import cadence and exception process.
The goal is not perfect automation for its own sake. The goal is confidence that the training scope matches the client workforce. A client report is only useful if users in scope are right.
This is where automated onboarding and multi-tenant management become operational requirements, not feature decoration.
4. Use a campaign spine, then adapt by risk
Do not give every client a blank-page campaign plan.
Create a standard campaign spine:
- Month 1: onboarding and acceptable use
- Month 2: phishing and reporting suspicious messages
- Month 3: password behavior and MFA
- Month 4: business email compromise and payment changes
- Month 5: safe file handling and data sharing
- Month 6: AI and sensitive information handling
- Month 7 onward: rotate based on threat, sector, and client risk
Then adapt by group. Finance, executives, privileged users, HR, developers, and frontline teams often need different examples.
The Australian Signals Directorate's ISM personnel security guidance makes this practical. It expects awareness training for all personnel, tailored content for specific groups, privileged user training, and a maintained awareness training register.
That is a useful pattern for MSPs: baseline for everyone, role-specific depth where risk is higher, and records good enough to prove it happened.
5. Make reminders boring and automatic
Reminder chasing is where MSP teams burn time without improving strategy.
Set reminders at known intervals before the due date, on the due date, and after the due date. Define who gets escalated and when. Keep the language plain. Give users one clear action.
Do not turn every overdue learner into a technician task. The system should handle routine nudges. The MSP should handle exceptions: VIP resistance, access problems, broken user scope, or client-side policy decisions.
CISA's phishing training guidance for businesses stresses ongoing education, reporting suspicious messages, and keeping employees informed between training events. That kind of cadence is much easier to maintain when reminders and updates are part of the delivery model.
6. Report for the client conversation, not the admin screen
An MSP report should answer the client's real questions fast.
At minimum, include:
- Coverage: users assigned, completed, overdue, excluded
- Cadence: campaign dates, due dates, reminders sent
- Content: modules or topics assigned
- Exceptions: users or groups needing attention
- Risk notes: patterns worth discussing, without overclaiming
- Evidence: export date, tenant name, campaign ID, completion record
- Next action: what the client needs to approve, enforce, or communicate
A technical admin view is not enough. A QBR owner needs a clean summary. An auditor may need exportable evidence. A business owner needs to know whether the program is under control.
This is why automated reports matter. The value is not the PDF itself. The value is removing the manual work between campaign activity and client-ready proof.
7. Price for coverage, not hesitation
Scaling fails when the MSP is punished for doing the right thing.
Per-seat pricing can make MSPs cautious. Every extra user changes cost. Every growing client becomes a margin question. Every quote needs a user count caveat.
That may be manageable for a single client. Across a client base, it creates friction at exactly the wrong point: when the MSP should be pushing full coverage.
Flat-fee economics make the operating model cleaner. The MSP can include training across the service base, avoid constant seat math, and treat user growth as expected service scope rather than a billing surprise.
That is the logic behind flat-fee awareness training and a clear fair use policy. It aligns the commercial model with the operational goal: cover the client fleet without making every new user a pricing event.
What good looks like when awareness training is scaled
A scaled MSP awareness program does not feel busy.
It feels controlled.
Here are the signs.
Client coverage is visible.
You can see which clients are active, which are paused, which have overdue campaigns, and which need attention. No one is asking a technician to remember which client was "waiting on a CSV."
Reports are ready before the client asks.
Monthly reports and QBR summaries are part of the service rhythm. The MSP is not building proof after the insurer sends a questionnaire.
User scope is trustworthy.
The roster reflects the client's current workforce well enough for the report to mean something. Exceptions are named, not hidden.
The baseline is consistent.
Every client gets the core awareness topics. Higher-risk users receive added training without derailing the standard delivery motion.
Admin time does not rise in a straight line with clients.
Adding the 30th client should not require the same work as adding the 3rd. If every new tenant creates the same manual load, the MSP has a capacity problem disguised as a training program.
Evidence is tenant-separated.
Client A's evidence does not mix with Client B's reports. That sounds obvious until someone tries to export proof from a single-tenant tool used 40 different ways.
Framework mapping for multi-client awareness training
Frameworks differ, but the pattern is consistent: define training, deliver it, tailor it where needed, track it, and improve it.
| Framework or guidance | What it expects | MSP delivery implication |
|---|---|---|
| NIST CSF 2.0 PR.AT | Personnel receive awareness and training for cybersecurity-related tasks | Keep a repeatable program for each tenant, not ad hoc annual videos |
| NIST PR.AT-01 examples | Train users on social engineering, reporting, acceptable use, basic cyber hygiene, testing, and refreshers | Include baseline topics, reminders, and periodic checks across clients |
| NIST SP 800-50 Rev. 1 | Build a lifecycle learning program with metrics and improvement | Treat awareness as a managed service motion, not a one-time assignment |
| CIS Control 14 | Maintain a program to influence secure behavior and reduce risk | Track program coverage, topic currency, and workforce participation |
| ISO/IEC 27001 | Manage information security risk across people, process, and technology | Connect training evidence to the client's ISMS and risk conversations |
| ASD ISM personnel security | Annual awareness training, tailored group content, privileged user training, and training register | Keep tenant-level registers and role-based training records |
| FTC small business guidance | Train staff regularly, update them on new risks, and track participation | Provide client-ready participation reporting and overdue visibility |
| CISA phishing guidance | Teach employees to recognize, verify, report, and delete suspicious messages | Make reporting behavior and phishing education part of the recurring campaign set |
Do not overstate what a training report proves. Completion evidence does not prove a client is secure. It proves the client has delivered assigned training to named users within a defined scope.
That is still valuable. It is the difference between "we think staff did something" and "here is the record."
Mistakes to avoid when scaling client awareness training
Mistake 1: Buying more content instead of fixing delivery
A larger library can help when clients need more topics. It does not solve setup, user scope, reminders, or reporting.
If the MSP's real pain is admin, the next purchase should be judged on delivery load, not only lesson count.
Mistake 2: Treating every client as a custom project
Custom work feels helpful at first. Then it becomes impossible to support.
The better model is a standard package with controlled variation: client branding, risk-based groups, framework notes, and optional add-ons. That keeps quality high without letting each client invent a new service model.
Mistake 3: Letting reporting happen after the fact
If evidence is assembled only when someone asks, the MSP is already behind.
Reports should be a byproduct of delivery. Every campaign should create a record of who was assigned, who completed, who did not, when reminders went out, and what content was covered.
Mistake 4: Hiding incomplete user scope
A clean-looking report with bad user data is worse than a messy report with honest exceptions.
Name the limits. If a client has not supplied a full roster, say so. If a user group is excluded, record it. If directory sync is not connected yet, make it visible.
Mistake 5: Charging in a way that discourages full coverage
If every added user is treated as a cost event, the MSP will be tempted to narrow scope.
That is bad security and bad service packaging. Awareness training works best when the default is full workforce coverage, with role-based additions where risk is higher.
How Defendwise fits
Defendwise is built for MSPs that want to package security awareness training across many clients without building a new admin queue for every tenant.
If your next growth problem is not content, but delivery, reporting, tenant separation, branding, and predictable margin, start with the Defendwise MSP platform and test the operating model against a real client rollout.
Frequently Asked Questions
How do MSPs deliver awareness training at scale for many clients?
MSPs deliver awareness training at scale by standardizing the operating model. That means reusable tenant setup, user lifecycle controls, standard campaign templates, automated reminders, client-ready reports, and exportable evidence.
The key is to avoid rebuilding the workflow for every client.
What is the biggest barrier to scaling security awareness training across clients?
The biggest barrier is usually admin drag, not lack of content. User changes, reminders, reporting, branding, and evidence export become expensive when repeated across many tenants.
A large content library can still fail if the MSP delivery model is manual.
Why is multi-tenant security awareness training important for MSPs?
Multi-tenant security awareness training gives the MSP one operating layer for many separate client environments. It helps keep user lists, reports, branding, and evidence separated while reducing portal switching and duplicate setup.
Without tenant separation, scaling often creates reporting risk and avoidable admin work.
How often should client awareness training run?
Most clients should receive training at onboarding and at least annually, with updates when threats, systems, policies, or roles change. Many MSPs also run shorter monthly or quarterly campaigns so awareness stays current.
Higher-risk users, such as finance, executives, admins, and privileged users, may need more targeted training.
What reports should an MSP provide for client awareness training?
A useful report shows assigned users, completed users, overdue users, excluded users, campaign dates, reminders, topics covered, and any follow-up actions. For audit or insurance requests, the report should also identify the tenant, export date, campaign scope, and evidence source.
The best report is readable by a business owner and detailed enough for a compliance reviewer.
Can awareness training be scaled without making it generic?
Yes. Standardize the delivery spine, then adapt the topics and examples by client risk. Baseline cyber hygiene can be common across clients, while finance, HR, executives, admins, and other high-risk groups receive more specific training.
That gives the MSP scale without flattening every client into the same program.
How does Defendwise help MSPs scale awareness training?
Defendwise gives MSPs a flat-rate, white-label, multi-tenant way to package awareness training across many clients. It is designed for MSPs that want predictable margin, clean tenant management, and recurring reporting without pricing every user as a separate event.
Learn more at defendwise.com.