Custom security awareness campaigns for MSPs
Custom security awareness campaigns help MSPs tailor training by client risk without rebuilding the program every month.
DefendWise
DefendWise
TL;DR
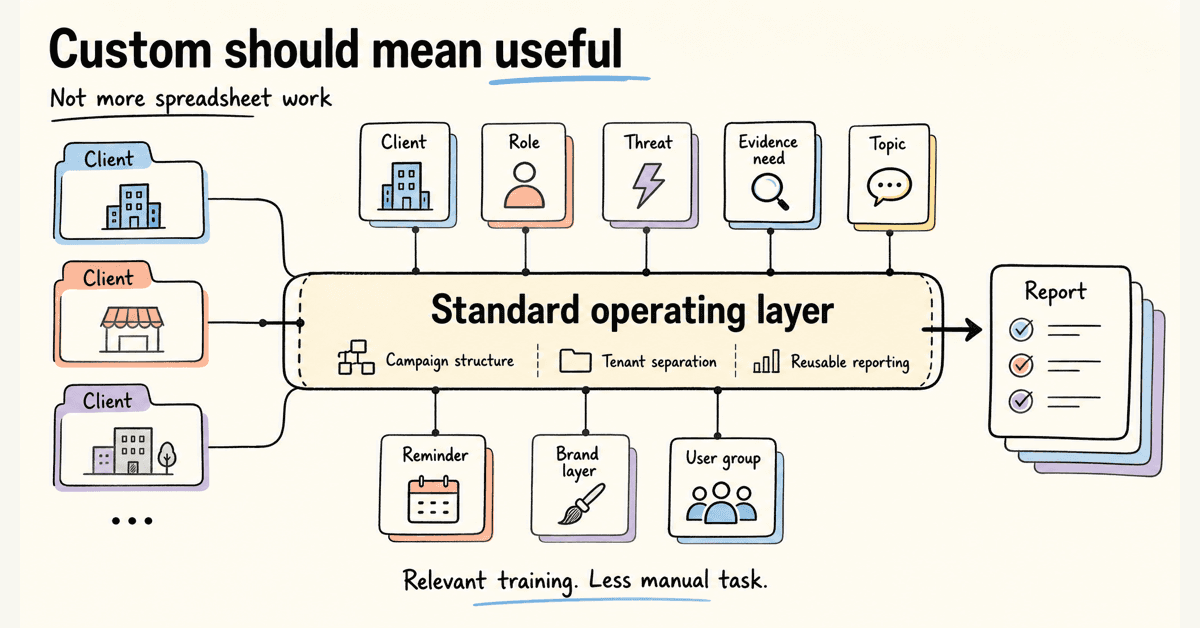
Custom security awareness campaigns tailor training to the client, role, threat, and evidence need.
That sounds simple until an MSP has to run it across 20, 50, or 100 clients. Every custom topic, reminder, brand layer, user group, and report can become another manual task.
The better model is a standard operating layer with client-specific edges: consistent campaign structure, clean tenant separation, reusable reporting, and enough customization to make the training feel relevant.
Custom should mean more useful for the client. It should not mean more spreadsheet work for the MSP.
What custom security awareness campaigns mean
A custom security awareness campaign is a training campaign adapted to a specific audience.
That can mean:
- Client-specific branding.
- Role-based topics.
- Industry-specific examples.
- Phishing simulations tied to current threats.
- Different cadences by risk group.
- Custom reminders and escalation paths.
- Evidence mapped to a client audit, cyber insurance renewal, or QBR.
The keyword is relevant, not decorative.
Changing the logo on the same annual module is branding. It is not a real custom campaign.
A real custom campaign connects the training to the client’s risk. Finance staff see invoice and payment-change fraud. Executives see impersonation and approval pressure. New starters see password, MFA, and reporting basics before bad habits set in. Service desk users see credential handling, identity checks, and social engineering pressure.
NIST SP 800-50 Rev. 1, published in September 2024, frames cybersecurity and privacy learning around behavior change, security culture, privacy culture, role-based needs, and metrics in Building a Cybersecurity and Privacy Learning Program.
That is the point of customization.
Not more content.
Better fit.
For an MSP, the commercial question is sharper: can you deliver that fit without turning every client into a one-off project?
Why custom security awareness campaigns matter for MSP clients
Most clients do not need a theatrical training program.
They need employees to spot the attacks they are likely to see, report them quickly, and give the business enough evidence to satisfy management, insurers, and auditors.
That is why generic annual training struggles.
Threats change faster than annual modules
CISA’s small-business phishing guidance says threats evolve constantly and once-a-year training is not enough. It also tells businesses to make sure employees know to whom and how to report suspicious emails or phishing attempts in Teach Employees to Avoid Phishing.
The same CISA page cites the FBI’s 2024 Internet Crime Report and notes phishing topped the five most reported cybercrimes, with 193,407 complaints.
That does not mean every client needs a weekly phishing lecture.
It means stale examples are a problem.
A campaign written around last year’s fake parcel scam may not prepare a finance user for a payment-change request, a QR-code lure, a fake Microsoft 365 prompt, or an AI voice call pretending to be a director.
Custom campaigns let MSPs adjust the examples without rebuilding the whole program.
Roles face different pressure
NIST CSF 2.0 includes awareness and training inside the Protect function. PR.AT-01 covers general awareness and training. PR.AT-02 covers individuals in specialized roles receiving awareness and training for those roles, as shown in the NIST CSF 2.0 publication and summarized by CSF Tools for PR.AT-01 and PR.AT-02.
That is useful for MSPs because it gives role-based customization a standards-backed rationale.
A receptionist, CFO, field technician, HR manager, and domain admin should not all receive the same training plan forever.
They share a baseline. They do not share the same risk surface.
Clients want evidence, not just activity
The FTC’s small-business cybersecurity guidance tells businesses to train staff on a regular schedule, update employees as new risks appear, and track employee participation in Cybersecurity for Small Business.
That matters for MSPs because the client does not only ask, “Did training happen?”
They ask:
- Who was included?
- Who finished?
- Who is overdue?
- What topics were covered?
- What changed after the campaign?
- Can I show this to an insurer or auditor?
Custom campaigns need clean evidence. Otherwise the MSP gets stuck chasing screenshots at renewal time.
What MSPs should customize
MSPs do not need to customize everything.
That is how a training program becomes a margin leak.
Start with the parts where customization changes the outcome.
| Campaign layer | What to customize | Why it matters for MSPs | Evidence to keep |
|---|---|---|---|
| Branding | Client logo, sender identity, portal or report presentation where supported | Makes the service feel client-owned while the MSP still runs the operating layer | Brand settings, client report exports, campaign screenshots if needed |
| Audience | Groups, roles, departments, high-risk users, new starters | Keeps training relevant without assigning every topic to every user | Assignment roster, group rules, user status |
| Topic | Phishing, BEC, MFA fatigue, QR phishing, AI voice scams, data handling, password hygiene | Matches current risk and client industry | Module list, campaign summary, topic coverage |
| Cadence | Onboarding, monthly, quarterly, annual, event-triggered | Prevents the “annual training and forget it” pattern | Campaign dates, due dates, reminder history |
| Simulation | Lure type, difficulty, target group, reporting path | Lets MSPs test behavior, not only completion | Clicks, reports, time to report, repeat failures |
| Reminders | Tone, timing, escalation, manager notifications | Reduces manual chasing by service teams | Reminder logs, overdue list, escalation record |
| Reporting | Client-level summary, QBR view, audit export, insurer packet | Turns training into proof clients can use | Completion report, evidence export, source notes |
This is the operating line:
Customize the client experience. Standardize the MSP workflow.
If every client requires a new campaign structure, new reminder logic, new report format, and new export process, the MSP is not scaling a service.
It is running small projects under a recurring invoice.
How to build custom campaigns without custom admin
A custom campaign should start with a repeatable runbook.
The goal is not to remove judgment. The goal is to stop rebuilding the boring parts.
1. Start with a campaign spine
Create a standard campaign structure before you customize anything.
For example:
- Baseline onboarding for all users.
- Monthly or quarterly threat update.
- Role-based add-ons for finance, executives, HR, admins, and service desk.
- Phishing or social engineering simulation where appropriate.
- Client-ready report and next action.
This makes customization manageable.
The client gets relevant training. The MSP keeps a consistent delivery model.
2. Segment by risk, not by org chart alone
Departments matter, but risk does not always follow the org chart.
Group users by what attackers can pressure them to do.
Useful groups include:
- Finance users who can approve, change, or query payments.
- Executives and owners whose names are used in impersonation.
- HR users handling employee data and documents.
- Service desk users handling passwords, MFA, and identity checks.
- Admins with privileged access.
- New starters.
- Repeat clickers or repeat non-reporters.
This is where role-based training earns its place.
A finance user does not need a generic warning about “being careful online.” They need to know how payment-change fraud works, how to verify a request out-of-band, and what to do if the request looks urgent.
3. Map topics to current threats
Custom campaigns should move as the threat mix moves.
The Verizon 2025 Data Breach Investigations Report analyzed 22,052 incidents and 12,195 confirmed breaches. It reports human involvement in breaches at about 60% in the 2025 dataset in the 2025 DBIR.
That is not a promise that training prevents 60% of breaches.
It is a reminder that people remain part of the attack path. Credentials, phishing, social engineering, misuse, and mistakes all show up in ways clients understand.
For MSP campaigns, that means topic selection should not be static.
Build a short topic backlog:
- Credential phishing.
- MFA fatigue and prompt bombing.
- Business email compromise.
- Invoice and payment-change fraud.
- QR phishing.
- SMS phishing.
- AI voice impersonation.
- Dangerous attachments.
- Secure reporting habits.
- Data handling for regulated clients.
Then pick topics by client risk, not by what is easiest to send.
4. Keep reporting standard across clients
This is where many MSP programs go sideways.
The campaign looks custom to the client, but the report should follow a standard evidence model.
Every client report should answer:
- Which users were assigned?
- Which users completed?
- Which users are overdue?
- What topics were covered?
- What reminders or escalations were sent?
- What simulation results matter?
- What changed since last report?
- What action should happen next?
ENISA’s awareness report includes recommendations around measuring cybersecurity behavior and planning awareness campaigns in Raising Awareness of Cybersecurity.
That is the reporting lesson for MSPs: custom campaigns still need measurable outcomes.
If the report has to be manually stitched together every month, the program will eventually get skipped, delayed, or delivered late.
5. Separate tenants cleanly
A custom campaign across multiple clients needs strict client separation.
The MSP should not have to worry about mixed reports, wrong branding, wrong recipients, or one client’s users showing up in another client’s evidence pack.
If you are using a single-tenant training tool across many clients, this can become a hidden admin cost.
You can still make it work. But the MSP needs to budget for the operational drag: client setup, user imports, branding, reminders, reporting, exports, and cleanup.
A multi-tenant SAT operating layer should make this simpler by keeping each client distinct while letting the MSP manage the program from one place.
6. Build reminders before the campaign starts
Reminders are not an afterthought.
They are part of the campaign design.
Decide before launch:
- When the first reminder sends.
- How many reminders are acceptable.
- Who gets escalated.
- Whether managers are involved.
- What happens to overdue users.
- What the MSP reports at the end.
Without that, custom campaigns become ticket queues.
The MSP launches the training, then spends the next 3 weeks chasing late users.
That is not a training strategy. It is admin with better branding.
7. Review, refine, and reuse
After the campaign, do not only file the completion report.
Review what happened:
- Did the right users get included?
- Was the topic relevant?
- Did completion drag in one group?
- Did users report suspicious messages?
- Did high-risk roles behave differently?
- Did the client understand the report?
- What should change next month or next quarter?
Then reuse what worked.
The MSP advantage is not endless custom drafting. It is building a stronger service pattern with every client campaign.
What good custom security awareness campaigns look like
Good custom campaigns are not loud.
They are specific, repeatable, and easy to prove.
The training feels relevant
Users should recognize the situations.
A finance user should see a realistic payment-change request. A managing partner should see executive impersonation. A new starter should see the reporting process before they need it.
If every module feels like generic cyber advice, the campaign is not custom in any meaningful way.
The MSP can run it across clients
Custom work that only works for 1 client is consulting.
That can be fine when the client pays for it.
But if custom security awareness campaigns are part of a managed service package, the MSP needs a repeatable operating model.
That means reusable templates, role groups, campaign cadence, automated onboarding, and report flows that do not require a new build every time.
The client gets proof
A custom campaign should produce client-ready evidence.
At minimum:
- Campaign name and date.
- Topic and audience.
- User assignment list.
- Completion status.
- Overdue users.
- Reminder history.
- Simulation summary if included.
- Next action.
For compliance-heavy clients, connect the evidence to the right framework expectation without overclaiming. Training evidence supports a control conversation. It does not prove the entire framework is satisfied.
A good automated reporting workflow turns this into a repeatable service output instead of a month-end scramble.
The economics still work
This is the part MSPs should say out loud.
Custom campaigns can improve client value. They can also destroy margin if the tool charges per seat and the MSP still has to manually manage every campaign.
Ask 2 questions before standardizing on a vendor:
- What happens to our bill when client seat counts grow?
- What happens to our admin workload when campaign count grows?
Per-seat pricing can be workable for some buyers. The issue for MSPs is that it ties training cost to client growth, while the MSP is often trying to bundle SAT into a fixed monthly service.
Flat pricing changes that math. If you are evaluating campaign customization as a packaged MSP service, include flat-fee SAT economics in the buying decision.
How custom campaigns map to security frameworks and guidance
Custom campaigns are not only a content decision.
They can support recognized awareness and training expectations when the evidence is clean.
| Source | What it supports | MSP campaign takeaway |
|---|---|---|
| NIST SP 800-50 Rev. 1 | Cybersecurity and privacy learning program, behavior change, role-based needs, metrics | Build campaigns around audience, role, behavior, and evaluation, not only content completion |
| NIST CSF 2.0 PR.AT-01 and PR.AT-02 | General awareness and specialized-role awareness/training | Keep a baseline for all users and add role-based campaigns for risky groups |
| CIS Control 14 | Establishing and maintaining a security awareness and skills training program | Show cadence, topic coverage, and participation evidence for each client |
| CISA phishing guidance | Phishing recognition, reporting, and regular reinforcement | Include reporting instructions and update campaigns as threats shift |
| FTC small-business guidance | Regular staff training, updates on new risks, participation tracking | Keep campaign records clean enough for client management and renewal discussions |
| ENISA awareness guidance | Planning campaigns and measuring cybersecurity behavior | Treat awareness as a measurable program, not a one-off content send |
CIS Control 14 says the purpose of a security awareness program is to educate the enterprise workforce on how to interact with assets and data securely in Security Awareness and Skills Training. Its assessment specification includes evidence concepts such as whether training is current, delivered at hire, and reviewed in the CIS Controls Assessment Specification for Control 14.
For MSPs, the message is straightforward.
If you customize campaigns, keep the evidence structured.
If the evidence is messy, the custom work will not survive the first audit, insurance renewal, or QBR challenge.
Common mistakes with custom security awareness campaigns
Mistake 1: Customizing everything
Too much customization breaks the service model.
If every client has a different campaign structure, report format, cadence, reminder flow, and naming convention, the MSP has created operational debt.
Customize the parts that affect relevance. Standardize the parts that protect margin.
Mistake 2: Treating branding as the whole campaign
White-label delivery matters.
Clients often want training that looks like part of their service experience, not a random third-party portal.
But branding is only the wrapper. The campaign still needs relevant topics, user groups, cadence, reminders, and evidence.
A white-label SAT layer is strongest when it supports the MSP service model, not when it hides a generic campaign underneath.
Mistake 3: Reporting blended averages
Fleet averages are useful for MSP operations.
They are weak client evidence.
A client does not care that the MSP’s whole client base had 94% completion if their own finance team is 61% complete and the CFO is overdue.
Report by client. Then report by risk group where needed.
Mistake 4: Sending stale examples
Attackers update their lures. Campaigns should update too.
CISA’s phishing page is blunt about this: threats evolve constantly, and staff need regular reinforcement.
If the training examples feel old, users learn to pass the module instead of recognize the threat.
Mistake 5: Forgetting the reporting path
A campaign that teaches users to spot suspicious activity but does not tell them how to report it is incomplete.
CISA, FTC, and phishing guidance all point back to reporting, escalation, and regular reinforcement.
Every custom campaign should answer the user’s practical question:
“What do I do next if this happens?”
Mistake 6: Making custom campaigns impossible to price
MSPs need margin discipline.
If every client request becomes unpaid custom content work, the SAT service becomes hard to package.
Define what is included:
- Standard onboarding campaign.
- Standard monthly or quarterly campaign.
- Role-based add-ons.
- Report format.
- Reasonable client branding.
- Extra custom work as a scoped project where needed.
That protects the client and the MSP.
How Defendwise fits
If you are choosing a SAT platform for custom campaigns, do not start with the content library size.
Start with the operating model.
Ask:
- Can we manage clients separately without duplicating admin?
- Can we make training feel client-specific without creating a one-off build every month?
- Can we report completion, overdue users, reminders, and evidence by client?
- Can we support role-based campaigns without losing track of who got what?
- Can we bundle this into our MSP service without the bill growing every time a client adds seats?
Defendwise is built for MSPs that want flat-rate security awareness training, unlimited users, white-label delivery, multi-tenant management, automated onboarding, and recurring reporting.
If custom security awareness campaigns are part of your buying checklist, start with Defendwise, then test the workflow against the questions above.
Do not buy a customization promise.
Ask to see the operating layer.
Frequently asked questions
What are custom security awareness campaigns?
Custom security awareness campaigns are training programs adapted to a specific audience, risk profile, client environment, role, threat, or compliance need.
For MSPs, the hard part is not creating one custom campaign. It is managing many client-specific campaigns without losing tenant separation, evidence quality, or margin.
Are custom security awareness campaigns better than standard training?
Custom campaigns can be better when the customization matches real risk.
Examples include finance fraud, executive impersonation, new-starter onboarding, QR phishing, AI voice scams, or industry-specific data handling. They are not better when every client receives a lightly renamed version of the same generic module.
How should MSPs customize security awareness training by client?
Start with a reusable campaign spine, then adapt the parts that matter: topics, user groups, client branding, cadence, reminders, escalation, and reporting.
Keep the evidence model standard so every client gets clean proof without manual rebuilding.
What should be included in a role-based security awareness campaign?
A role-based campaign should include the threats, decisions, and reporting paths that role actually faces.
Finance needs invoice fraud and payment-change verification. Executives need impersonation and approval pressure. Service desk users need credential handling and identity checks.
How often should security awareness campaigns be updated?
Annual training is not enough for fast-moving threats.
A useful MSP program has recurring campaigns, fresh threat updates, and client reporting that shows what changed. The exact cadence depends on client risk, service tier, and compliance needs.
How do custom campaigns support compliance evidence?
Custom campaigns can support compliance evidence when they show who was assigned, what was covered, when training happened, completion status, overdue users, reminders, and report exports.
They should not be treated as a compliance guarantee by themselves. Training evidence supports the control conversation.
How does Defendwise fit into custom security awareness campaigns?
Defendwise is built for MSPs that need flat-fee security awareness training, unlimited users, white-label delivery, multi-tenant management, automated onboarding, and recurring reporting.
If custom campaigns are part of your buying checklist, test how the platform handles client-specific topics, branding, reminders, and evidence exports before you commit.
Source notes
External source URLs used or checked:
- https://csrc.nist.gov/pubs/sp/800/50/r1/final
- https://nvlpubs.nist.gov/nistpubs/CSWP/NIST.CSWP.29.pdf
- https://csf.tools/reference/nist-cybersecurity-framework/v2-0/pr/pr-at/pr-at-01/
- https://csf.tools/reference/nist-cybersecurity-framework/v2-0/pr/pr-at/pr-at-02/
- https://www.cisecurity.org/controls/security-awareness-and-skills-training
- https://cas.docs.cisecurity.org/en/latest/source/Controls14/
- https://www.cisa.gov/audiences/small-and-medium-businesses/secure-your-business/teach-employees-avoid-phishing
- https://www.cisa.gov/sites/default/files/2023-10/Phishing%20Guidance%20-%20Stopping%20the%20Attack%20Cycle%20at%20Phase%20One_508c.pdf
- https://www.ftc.gov/business-guidance/small-businesses/cybersecurity
- https://www.ftc.gov/system/files/attachments/phishing/cybersecurity_sb_phishing.pdf
- https://www.enisa.europa.eu/publications/raising-awareness-of-cybersecurity
- https://www.verizon.com/business/resources/T16f/reports/2025-dbir-data-breach-investigations-report.pdf
- https://www.ic3.gov/AnnualReport/Reports/2024_IC3Report.pdf